Suspected NK attackers hack into S. Korea's cyber command through main server
Military investigators looking into the first hacking of South Korea's cyber command intranet said Wednesday the suspected North Korean attackers accessed the network through a server in the defense ministry's main information center.
The findings raised concerns that confidential information may have been compromised as the affected server is connected with the information systems of the Army, Navy and the Air Force. But the ministry said information saved on the server was not stolen.
The Ministry of National Defense said a total of 3,200 computers, including 700 linked with the intranet, were contaminated with malware in the latest cyber attack, which occurred on Aug. 4.
It said some military documents were hacked while refusing to provide details. The computer used by Defense Minister Han Min-koo was also affected, the official said.
On Tuesday, the ministry said the IP addresses linked to the attack were traced to a location in China that has been used by North Korean hackers.
"As one of the military's two integration servers was jointly linked to the internet and the intranet, it allowed the hackers to gain access to the intranet," a ministry official said.
It is one of two servers the military operates. The other server involves information for the defense ministry, the Defense Security Command and the Defense Acquisition Program Administration (DAPA).
"We are still in the process of determining what data were leaked. We found the hackers infiltrated the intranet using the main server but information in the server remains intact," the official said.
The cyber command separated the affected server from the whole network to avoid the spread of viruses in October, two months after the initial hacking attempt was made in August.
It marked the first time that the data of South Korea's cyber command has been compromised. South Korea set up the command in January 2010 as part of its efforts to counter external hacking attempts on the country's military.
North Korea -- which has thousands of cyberwarfare personnel -- has a track record of waging cyberattacks on South Korea and the United States in recent years, though it has flatly denied any involvement.
Earlier this year, Seoul accused North Korea of stealing information from about 10 South Korean officials by hacking into their smartphones.
Two months ago, Rep. Kim Jin-pyo, a lawmaker of the main opposition Democratic Party, claimed that the cyber command was hacked in September. He told Yonhap that the attack targeted the "vaccine routing server" installed at the cyber command.
Kim, who is a member of the parliament's national defense committee, said that a malicious code was identified and it appears to have taken advantage of the vulnerability of the routing server.
The server is tasked with security on computers that the military has for internet-connection purposes. Around 20,000 military computers are known to have been connected to the server.
Kim said in October that chances are "very low" that the hacking led to a leak of confidential information, given that the military's intranet is not connected to the server.
The defense ministry later announced it has identified the intrusion of the malicious code into the system. (Yonhap)
The findings raised concerns that confidential information may have been compromised as the affected server is connected with the information systems of the Army, Navy and the Air Force. But the ministry said information saved on the server was not stolen.
The Ministry of National Defense said a total of 3,200 computers, including 700 linked with the intranet, were contaminated with malware in the latest cyber attack, which occurred on Aug. 4.
It said some military documents were hacked while refusing to provide details. The computer used by Defense Minister Han Min-koo was also affected, the official said.
On Tuesday, the ministry said the IP addresses linked to the attack were traced to a location in China that has been used by North Korean hackers.
"As one of the military's two integration servers was jointly linked to the internet and the intranet, it allowed the hackers to gain access to the intranet," a ministry official said.
It is one of two servers the military operates. The other server involves information for the defense ministry, the Defense Security Command and the Defense Acquisition Program Administration (DAPA).
"We are still in the process of determining what data were leaked. We found the hackers infiltrated the intranet using the main server but information in the server remains intact," the official said.
The cyber command separated the affected server from the whole network to avoid the spread of viruses in October, two months after the initial hacking attempt was made in August.
It marked the first time that the data of South Korea's cyber command has been compromised. South Korea set up the command in January 2010 as part of its efforts to counter external hacking attempts on the country's military.
North Korea -- which has thousands of cyberwarfare personnel -- has a track record of waging cyberattacks on South Korea and the United States in recent years, though it has flatly denied any involvement.
Earlier this year, Seoul accused North Korea of stealing information from about 10 South Korean officials by hacking into their smartphones.
Two months ago, Rep. Kim Jin-pyo, a lawmaker of the main opposition Democratic Party, claimed that the cyber command was hacked in September. He told Yonhap that the attack targeted the "vaccine routing server" installed at the cyber command.
Kim, who is a member of the parliament's national defense committee, said that a malicious code was identified and it appears to have taken advantage of the vulnerability of the routing server.
The server is tasked with security on computers that the military has for internet-connection purposes. Around 20,000 military computers are known to have been connected to the server.
Kim said in October that chances are "very low" that the hacking led to a leak of confidential information, given that the military's intranet is not connected to the server.
The defense ministry later announced it has identified the intrusion of the malicious code into the system. (Yonhap)
(责任编辑:关于我们)
推荐文章
-
First officially approved Gen IV nuclear reactor in the US breaks ground
 Kairos Power has broken ground at Oak Ridge on the first officially approved Generation IV reactor e
...[详细]
Kairos Power has broken ground at Oak Ridge on the first officially approved Generation IV reactor e
...[详细]
-
 【上市公司动态】1.12月3日晚间,山西汾酒(600809)发布公告称,为进一步提升公司市场竞争力和盈利能力,同时解决汾酒集团全资子公司杏花村国贸与公司的同业竞争问题,公司全资子公司汾酒国贸拟支付现金
...[详细]
【上市公司动态】1.12月3日晚间,山西汾酒(600809)发布公告称,为进一步提升公司市场竞争力和盈利能力,同时解决汾酒集团全资子公司杏花村国贸与公司的同业竞争问题,公司全资子公司汾酒国贸拟支付现金
...[详细]
-
 “没想到咱青岛的港这么大、这么先进,真是太震撼了!”“下次再有机会,我要带着孩子一块来港上见识见识,确实让人很自豪!”12月24日,以“庆祝
...[详细]
“没想到咱青岛的港这么大、这么先进,真是太震撼了!”“下次再有机会,我要带着孩子一块来港上见识见识,确实让人很自豪!”12月24日,以“庆祝
...[详细]
-
鎷涘晢閾惰鍙戝敭钀岀郴鐔婄尗甯佲€滃ぇ鑴哥尗鈥漘涓浗灞变笢缃慱闈掑矝
 銆€銆€杩戞湡锛屾嫑鍟嗛摱琛屽彂鍞?018骞磋悓绯荤唺鐚竵“澶ц劯鐚?rdquo;銆傝鐔婄尗甯佸睘浜庝汉姘戝竵浣撶郴锛屾槸鎴戝浗娉曞畾璐у竵锛屽畨鍏ㄤ繚鍊笺€傝甯侀潰涓虹唺鐚舰璞★
...[详细]
銆€銆€杩戞湡锛屾嫑鍟嗛摱琛屽彂鍞?018骞磋悓绯荤唺鐚竵“澶ц劯鐚?rdquo;銆傝鐔婄尗甯佸睘浜庝汉姘戝竵浣撶郴锛屾槸鎴戝浗娉曞畾璐у竵锛屽畨鍏ㄤ繚鍊笺€傝甯侀潰涓虹唺鐚舰璞★
...[详细]
-
Nvidia GeForce Now Ultimate vs. New Graphics Card
Video games are getting prettier. But the price that comes with more realistic graphics, ray tracing ...[详细]
-
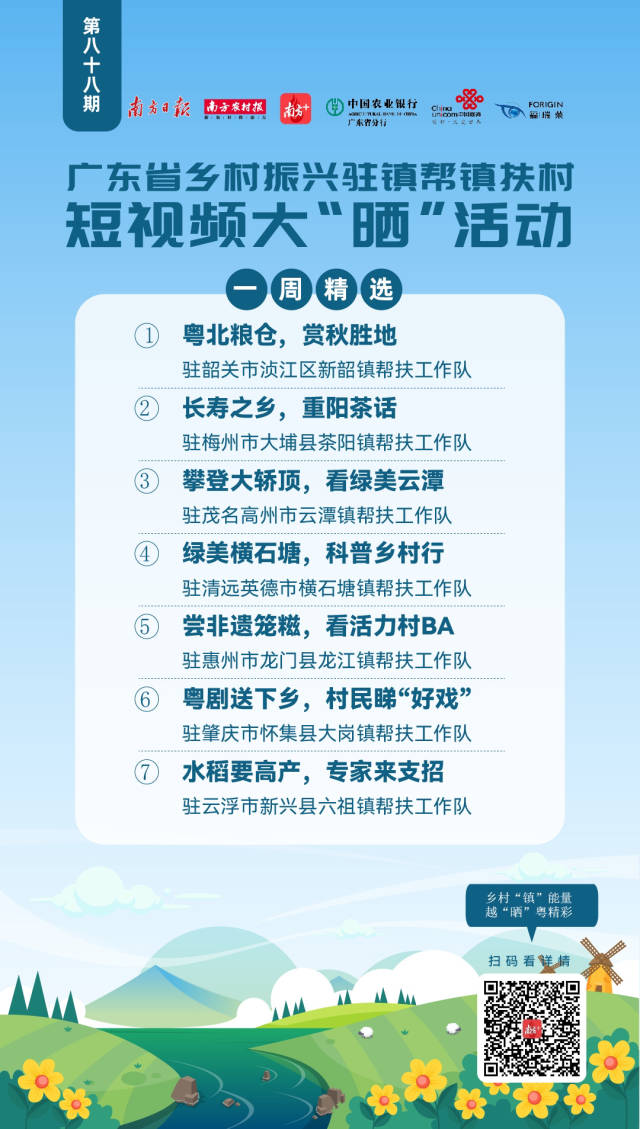 粤北粮仓 赏秋胜地 | 驻镇帮镇扶村短视频大“晒”一周精选88)_南方+_南方plus以“乡村‘镇’能量,越‘晒’粤精彩”为主题的广东省乡村振兴驻镇帮镇扶村短视频大“晒”活动于2022年2月全面启动。
...[详细]
粤北粮仓 赏秋胜地 | 驻镇帮镇扶村短视频大“晒”一周精选88)_南方+_南方plus以“乡村‘镇’能量,越‘晒’粤精彩”为主题的广东省乡村振兴驻镇帮镇扶村短视频大“晒”活动于2022年2月全面启动。
...[详细]
-
 第五届中国工业大奖获奖名单近日正式揭晓,全国46家企业、37个项目被授予不同级别奖项。我市的青特集团有限公司和青岛琅琊台集团股份有限公司的衣康酸生物关键技术研究及产业化项目获得中国工业大奖表彰奖,青岛
...[详细]
第五届中国工业大奖获奖名单近日正式揭晓,全国46家企业、37个项目被授予不同级别奖项。我市的青特集团有限公司和青岛琅琊台集团股份有限公司的衣康酸生物关键技术研究及产业化项目获得中国工业大奖表彰奖,青岛
...[详细]
-
 雅安发展投资有限责任公司以下简称:雅投公司)突出国企特色、突出学史力行、突出担当作为,扎实推进党史学习教育,围绕群众需求办实事,把学习教育成果转化为推动发展、改善民生的强大动力和工作实效。关爱特殊儿童
...[详细]
雅安发展投资有限责任公司以下简称:雅投公司)突出国企特色、突出学史力行、突出担当作为,扎实推进党史学习教育,围绕群众需求办实事,把学习教育成果转化为推动发展、改善民生的强大动力和工作实效。关爱特殊儿童
...[详细]
-
 本报讯近日,市教育局班子成员碰头会召开,听取近期有关工作落实情况汇报,安排部署下一步重点工作。会议要求,要狠抓工作落实,全面推进教育各项工作。全力推进川西教育中心建设,扎实开展省、市示范性普通高中、义
...[详细]
本报讯近日,市教育局班子成员碰头会召开,听取近期有关工作落实情况汇报,安排部署下一步重点工作。会议要求,要狠抓工作落实,全面推进教育各项工作。全力推进川西教育中心建设,扎实开展省、市示范性普通高中、义
...[详细]
-
 中国山东网-感知山东青岛12月25日讯(记者 姜婷 通讯员 丁帅) 为丰富青岛航空航线网络,给烟台和长春两地市民提供更多出行便利,青岛航空于12月24日新增了烟台=长春往返航线。该航线由全新空客A32
...[详细]
中国山东网-感知山东青岛12月25日讯(记者 姜婷 通讯员 丁帅) 为丰富青岛航空航线网络,给烟台和长春两地市民提供更多出行便利,青岛航空于12月24日新增了烟台=长春往返航线。该航线由全新空客A32
...[详细]
热点阅读
随机内容

 Ruling bloc seeks tougher sentences for deepfake sex crimes
Ruling bloc seeks tougher sentences for deepfake sex crimes 20家重点商贸企业元旦实现销售7.2亿元
20家重点商贸企业元旦实现销售7.2亿元 我市16675名学生参加中考
我市16675名学生参加中考 提升“获得电力”服务水平 持续改善用电营商环境
提升“获得电力”服务水平 持续改善用电营商环境 全国土壤普查办抽验组到广东开展土壤普查质量抽验
全国土壤普查办抽验组到广东开展土壤普查质量抽验
